Wireless networks are accessible to anyone within the router’s transmission radius. This makes them vulnerable to attacks. Hotspots are available in public places such as airports, restaurants, parks, etc.
In this tutorial, we will introduce you to common techniques used to exploit weaknesses in wireless network security implementations. We will also look at some of the countermeasures you can put in place to protect against such attacks.
Topics covered in this tutorial
What is a wireless network?
Basically, all you need is the MAC address when it comes to cracking WiFi passwords, but once you have control over the router, then knowing the IP is simple and important. Some routers have WPS (WiFi Protected Setup) support. There is a WPS PIN bruteforcing flaw that can be. Now it's time to pick your network. Run: airodump-ng (interface) To see a list of wireless networks around you. When you see the one you want, hit Ctrl+C to stop the list.
Mar 01, 2019 If you’ve noticed your Google Chrome or Mac acting weird, your machine may have a browser hijacker. There’s a variety of malware out there, but we’ll use a common and annoyingly persistent hijack called Kuklorest as an example. Try going to chrome.google.com/webstore. At the top u will see a gear, click it then my apps and extensions. See if it is listed. If it is there should be a remove option. Apr 24, 2019 The Chrome redirect virus is one example which, unusually, only affects Chrome browsers – though there are variants that affect other browsers too. Once on your Mac, it redirects your homepage and searches, displays intrusive adverts, and tries to direct you to more malware with fake alerts. Everything you need to know about Chrome redirect virus. https://golscripts.netlify.app/my-chrome-is-hacked-on-my-mac.html.
A wireless network is a network that uses radio waves to link computers and other devices together. The implementation is done at the Layer 1 (physical layer) of the OSI model.
How to access a wireless network?
You will need a wireless network enabled device such as a laptop, tablet, smartphones, etc. You will also need to be within the transmission radius of a wireless network access point. Most devices (if the wireless network option is turned on) will provide you with a list of available networks. If the network is not password protected, then you just have to click on connect. If it is password protected, then you will need the password to gain access.
Wireless Network Authentication
Since the network is easily accessible to everyone with a wireless network enabled device, most networks are password protected. Let’s look at some of the most commonly used authentication techniques.
WEP
WEP is the acronym for Wired Equivalent Privacy. It was developed for IEEE 802.11 WLAN standards. Its goal was to provide the privacy equivalent to that provided by wired networks. WEP works by encrypting the data been transmitted over the network to keep it safe from eavesdropping.
WEP Authentication
Open System Authentication (OSA) – this methods grants access to station authentication requested based on the configured access policy.
Shared Key Authentication (SKA) – This method sends to an encrypted challenge to the station requesting access. The station encrypts the challenge with its key then responds. If the encrypted challenge matches the AP value, then access is granted.

WEP Weakness
WEP has significant design flaws and vulnerabilities.
- The integrity of the packets is checked using Cyclic Redundancy Check (CRC32). CRC32 integrity check can be compromised by capturing at least two packets. The bits in the encrypted stream and the checksum can be modified by the attacker so that the packet is accepted by the authentication system. This leads to unauthorized access to the network.
- WEP uses the RC4 encryption algorithm to create stream ciphers. The stream cipher input is made up of an initial value (IV) and a secret key. The length of the initial value (IV) is 24 bits long while the secret key can either be 40 bits or 104 bits long. The total length of both the initial value and secret can either be 64 bits or 128 bits long.The lower possible value of the secret key makes it easy to crack it.
- Weak Initial values combinations do not encrypt sufficiently. This makes them vulnerable to attacks.
- WEP is based on passwords; this makes it vulnerable to dictionary attacks.
- Keys management is poorly implemented. Changing keys especially on large networks is challenging. WEP does not provide a centralized key management system.
- The Initial values can be reused
Because of these security flaws, WEP has been deprecated in favor of WPA
WPA
WPA is the acronym for Wi-Fi Protected Access. It is a security protocol developed by the Wi-Fi Alliance in response to the weaknesses found in WEP. It is used to encrypt data on 802.11 WLANs. It uses higher Initial Values 48 bits instead of the 24 bits that WEP uses. It uses temporal keys to encrypt packets.
Hacking Into Wifi Networks
WPA Weaknesses
- The collision avoidance implementation can be broken
- It is vulnerable to denial of service attacks
- Pre-shares keys use passphrases. Weak passphrases are vulnerable to dictionary attacks.
How to Crack Wireless Networks
WEP cracking
Cracking is the process of exploiting security weaknesses in wireless networks and gaining unauthorized access. WEP cracking refers to exploits on networks that use WEP to implement security controls. There are basically two types of cracks namely;
- Passive cracking– this type of cracking has no effect on the network traffic until the WEP security has been cracked. It is difficult to detect.
- Active cracking– this type of attack has an increased load effect on the network traffic. It is easy to detect compared to passive cracking. It is more effective compared to passive cracking.
WEP Cracking Tools
- Aircrack– network sniffer and WEP cracker. Can be downloaded from http://www.aircrack-ng.org/
- WEPCrack– this is an open source program for breaking 802.11 WEP secret keys. It is an implementation of the FMS attack. http://wepcrack.sourceforge.net/
- Kismet- this can include detector wireless networks both visible and hidden, sniffer packets and detect intrusions. https://www.kismetwireless.net/
- WebDecrypt– this tool uses active dictionary attacks to crack the WEP keys. It has its own key generator and implements packet filters. http://wepdecrypt.sourceforge.net/
WPA Cracking
WPA uses a 256 pre-shared key or passphrase for authentications. Short passphrases are vulnerable to dictionary attacks and other attacks that can be used to crack passwords. The following tools can be used to crack WPA keys.
- CowPatty– this tool is used to crack pre-shared keys (PSK) using brute force attack. http://wirelessdefence.org/Contents/coWPAttyMain.htm
- Cain & Abel– this tool can be used to decode capture files from other sniffing programs such as Wireshark. The capture files may contain WEP or WPA-PSK encoded frames. http://www.softpedia.com/get/Security/Decrypting-Decoding/Cain-and-Abel.shtml
General Attack types
- Sniffing– this involves intercepting packets as they are transmitted over a network. The captured data can then be decoded using tools such as Cain & Abel.
- Man in the Middle (MITM) Attack– this involves eavesdropping on a network and capturing sensitive information.
- Denial of Service Attack– the main intent of this attack is to deny legitimate users network resources. FataJack can be used to perform this type of attack. More on this in article
Cracking Wireless network WEP/WPA keys
It is possible to crack the WEP/WPA keys used to gain access to a wireless network. Doing so requires software and hardware resources, and patience. The success of such attacks can also depend on how active and inactive the users of the target network are.
Determine Supported IP ProtocolsDetermine which IP Protocols (TCP, UDP, ICMP, etc.) are supported by target host: $ nmap -sO 192.168.1.1 8. Scan For TCP/UDP PortsScan for All TCP Ports: $ nmap -sT 192.168.1.1Scan for Particular TCP Ports: $ nmap -p T:80 192.168.1.1Scan for All UDP Ports: $ nmap -sU 192.168.1.1Scan for Particular UDP Ports: $ nmap -p U:53 192.168.1.1Combine scanning of different ports: $ nmap -p U:53,79,113,T:21-25,80,443,8080 192.168.1.1 9. 192.168.1.1Scan for top most Common Ports: $ nmap -top-ports 5 192.168.1.1$ nmap -top-ports 10 192.168.1.1 7. https://golscripts.netlify.app/mac-address-spoof-hacking.html. Scan fewer ports than the default scan. Perform a Fast ScanEnable Fast Mode: $ nmap -F 192.168.1.1.
We will provide you with basic information that can help you get started. Backtrack is a Linux-based security operating system. It is developed on top of Ubuntu. Backtrack comes with a number of security tools. Backtrack can be used to gather information, assess vulnerabilities and perform exploits among other things.
May 13, 2017 Bypass mac address filter in Wifi network with Windows PC, MAC Hacking Trick. The MAC Address is a 12-digit hexadecimal number or 128 bit number which is used to individually identify a host on a network. Each NIC (Network Interface Card) has a unique MAC address (Media Access Control). https://golscripts.netlify.app/hacking-mac-filter-for-windows-10.html.
Some of the popular tools that backtrack has includes;
- Metasploit
- Wireshark
- Aircrack-ng
- NMap
- Ophcrack
Cracking wireless network keys requires patience and resources mentioned above. At a minimum, you will need the following tools
A wireless network adapter with the capability to inject packets (Hardware)
- Kali Operating System. You can download it from here https://www.kali.org/downloads/
- Be within the target network’s radius. If the users of the target network are actively using and connecting to it, then your chances of cracking it will be significantly improved.
- Sufficient knowledge of Linux based operating systems and working knowledge of Aircrack and its various scripts.
- Patience, cracking the keys may take a bit of sometime depending on a number of factors some of which may be beyond your control. Factors beyond your control include users of the target network using it actively as you sniff data packets.
How to Secure wireless networks
In minimizing wireless network attacks; an organization can adopt the following policies
- Changing default passwords that come with the hardware
- Enabling the authentication mechanism
- Access to the network can be restricted by allowing only registered MAC addresses.
- Use of strong WEP and WPA-PSK keys, a combination of symbols, number and characters reduce the chance of the keys been cracking using dictionary and brute force attacks.
- Firewall Software can also help reduce unauthorized access.
Hacking Activity: Crack Wireless Password
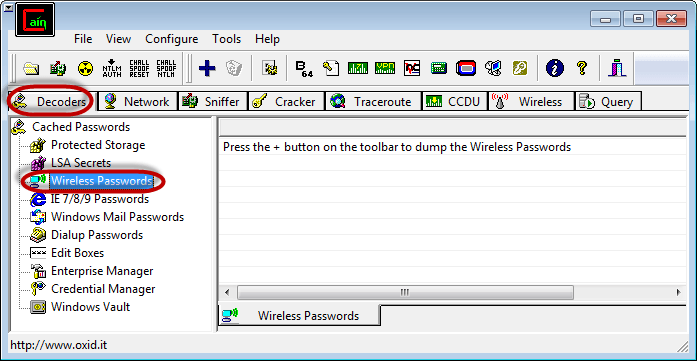
In this practical scenario, we are going touse Cain and Abel to decode the stored wireless network passwords in Windows. We will also provide useful information that can be used to crack the WEP and WPA keys of wireless networks.
Decoding Wireless network passwords stored in Windows
- Download Cain & Abel from the link provided above.
- Open Cain and Abel
- Ensure that the Decoders tab is selected then click on Wireless Passwords from the navigation menu on the left-hand side
- Click on the button with a plus sign
Hack Wireless Network Password
- Assuming you have connected to a secured wireless network before, you will get results similar to the ones shown below
- The decoder will show you the encryption type, SSID and the password that was used.
Summary
- Wireless network transmission waves can be seen by outsiders, this possesses many security risks.
- WEP is the acronym for Wired Equivalent Privacy. It has security flaws which make it easier to break compared to other security implementations.
- WPA is the acronym for Wi-Fi Protected Access. It has security compared to WEP
- Intrusion Detection Systems can help detect unauthorized access
- A good security policy can help protect a network.
This article is all about the question that everybody is right now asking on the internet, which is how to hack wifi password on laptop. We have discussed both the ways including how to do that without any software and with software. For the former, we're going to make use of the Windows built-in tool, command prompt. And for the latter, the software which we're going to utilize is called as PassFab Wifi Key, and this tool is a sure shot method to help you recover the wifi password. Let's not wait any further and get to explore these proven ways.
Go to Safari Preferences and reenable JavaScript in the Security prefs(alternatively you can do that in Terminal).Don’t forget this step, or you’ll think the web is broken!More sophisticated or persistent adware and malware attacks can be mitigated by using apps like my free or.You can force quit an app by pressing the following keys in combination on your keyboard then choosing the app you want to quit. Reopen SafariYou’ll get all your tabs back including the hijacked tab, but the pop up won’t appear, and you can now close the hijacked tab.3. https://golscripts.netlify.app/safari-hacked-on-mac.html.
Part 1: How to Hack Wi-Fi Password on Laptop without Any Software
The method that we are going to learn today will be working in Windows 10 and 8 but unfortunately this method is not supported by Windows 7. Follow the steps given below to know 'how to hack wifi password on laptop without any software'
- You need to go on the 'Start' button and type 'cmd' in the search bar. After that select 'Command Prompt' as admin so that you can access it faster.
- Once are done with the above process you need to type the following command.netsh wlan show profiles
- After that you will can see the list of networks on which you join with your computer.
- Now you need to type the following command in order to find the password of one network profile. Please keep in mind that you replace profilename with the name of the profile.netsh wlan show profile name=profilename key=clear
- Once you are done with the above process, find the 'Key Content' line which will be the password of that corresponding network.
So, this was all about how you can find you Wi-Fi password without any software. This method is very much effective if you are going to use it on windows 8 and 10. So what you are waiting for, go on and try on your computer.
Hacking A Wifi Network

Part 2: How to Hack Wi-Fi Password on Laptop in Minutes
There are lot of people searching this question on internet that 'how to hack wifi password on laptop', here is a software for you called PassFab Wifi Key, that will allow you to know 'how to hack wifi password on laptop'. With this software, how to hack wifi password on laptop is no big deal. With its one click process, even the non-tech savvy users can make use of this software effectively. Moreover, this software supports smooth execution on various Windows OS versions including Windows 7, 8 and 10 as well.
Hack Into Wifi Network Password
Here are the brief steps on how to use this powerful wireless password recovery tool:
Step 1. Launch Wifi Key
First thing is to download, install and start the PassFab Wifi Key software, this can be done in any computer that contains windows operating system or you can also do it in your surface tablet. Once you have opened this software, you can see the Wi-Fi password of each network.
Macs are not based on Linux in any way. MacOS is a true, certified UNIX (check with The Open Group to verify certifications) that is based on FreeBSD, NetNSD and OpenBSD. Linux is not a certified UNIX, it is a knockoff of Linux (as stated by Linux. My Mac has currently been hacked. I am finding out he is getting into all my bank accounts and changing the password and even 401k and trading accts. He is also attempting to hack my girlfriends computers as well as we speak. I think he got in through a hole i had with my smart tv, google WiFi, wenmo plugs, google home, Phillips hue lights etc. Screenshots on the Mac are pretty awesome, and there are three ways to take a screen shot with your Mac: Command + Shift + 4 and you’ll get a crosshair that you can drag with your mouse to capture exactly what you want.; Command + Shift + 4 at the same time and then let them go, then hit the Spacebar. Now you can click on any window you want and take a shot of that entire window, shadow. Once done, you won’t have to say again why is my Mac so slow. Keyboard responds slowly. Many users wondering why is my Mac so slow have reported that their keyboard freezes for sometimes while doing work. This lag makes productivity slow and poor. The biggest reason behind this issue is the outdated system caches. Why is it so hard to hack a macbook.
Step 2. Select Network Name
Once you have completed the above step you can directly copy the Wi-Fi password or you can also export the selected network that you want to save. Once you've selected the network you want to save click on the 'Export' button.
Step 3. Export Wi-Fi Password
Afterwards, you will see another window popping up and it will prompt you to save them (the network you wish to save) as the CSV files. Now, you need to navigate to the destination path where you want to save the file and then click on the 'Save' button. Within a couple of seconds, the file will be exported to the destination address. You can then access the exported CSV file that contains your wireless network information as and when needed.
You can also watch this video tutorial about how to hack Wi-Fi password on laptop using PassFab Wifi Key:
Hack Any Wifi Password Free
Conclusion
Hack Into Wifi Network Password
So, in this article we have discussed about 'how to hack wifi password on laptop without any software' and also with the help of software. The method which we are using to find wifi password without software is 'command prompt'. Here we have discussed about a Wifi password key program from PassFab, that will help you to find the wifi password. Hope this article would have helped you with solving your all queries related to the question that 'how to hack wifi password on laptop'.