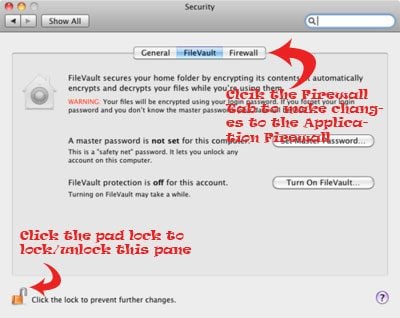
May 28, 2020 For iPhones, ensuring you phone isn’t jailbroken also prevents anyone from downloading a spy app to your phone, since such software – which tampers with system-level functions - doesn’t make. Aug 03, 2015 This way, if your Mac is stolen, they thieves won’t get access to your private data. Apple’s FileVault full disk encryption has been around for some time and it’s a great idea to turn this on. FileVault encrypts your entire hard drive using XTS-AES 128, a secure encryption algorithm.
Try these downloads recommended by Kim Komando to keep your PC or Mac safe. (iStock)
The FBI has seen a significant spike in cybercrime reports since the onset of the COVID-19 pandemic. Hackers, scammers, and snoops are having a field day. Be sure to check for any updates to your gear.
A bug has been found in 79 different popular router models that lets hackers remotely take over your devices. Tap or click here for the complete list of affected routers and how to protect your network.
Phones are targets, too. Tap or click here for a specialized app that will tell you if your iPhone has been hacked.
Although you’re frustrated over recent national events, it’s no time to let your guard down. Here a few ways to safeguard your digital life.
1. Use the internet anonymously
Are you tired of advertisers, snoops, and Big Tech tracking your every move online? One of the most popular inconspicuous tools available is The Onion Router or Tor, for short. Initially developed in the mid-1990s by the U.S. Navy to protect U.S. online communications, it is now a free global network for public use.
By rerouting your internet traffic through Tor, you can make it difficult for would-be snoops to trace your location and online activity back to you. From privacy advocates to journalists to internet denizens who are concerned about surveillance and monitoring, Tor is the go-to tool for web anonymity.
However, setting up your computer to exclusively route its traffic through Tor can be a challenge. Thankfully, there's an easy-to-use web browser that will automatically route all its traffic through Tor even without advanced computer and networking knowledge.
2. Don’t let malware take over your system
Antimalware programs are essential for scanning and removing harmful files from your computer. Microsoft’s Windows Defender comes with your PC. It scans your computer for malware, quarantines malicious files and removes them with just a few clicks.
Make sure you’re using the latest version. Tap or click here to get the latest Windows Defender updates.
Although Apple does not offer built-in malware protection for Macs, you still need it. In about 30 seconds, Malwarebytes for Mac identifies and removes malicious files. There is a pay version, but the free option is sufficient for most people.
3. Let IBM control your DNS
The internet’s Domain Name System (DNS) directs you to specific websites when you enter a domain name in your browser. It’s why you can type a site’s name (for example, Archive.org) rather than the site’s cumbersome IP address (207.241.224.2). Your internet service provider automatically assigns your DNS settings, but hackers can hijack them to redirect traffic to malicious websites.
Instead, use Quad9 maintained by IBM and The Global Cyber Alliance. Once set up, the free and fast DNS Quad9 service instantly checks any site you wish to visit against IBM X-Force’s threat intelligence database of over 40 billion analyzed webpages and images.
Quad9 blocks unauthorized DNS redirects and remote hosts, too. It's simple to set up, and there is no program to download.
4. Make sure no one is spying on you
Keyloggers collect everything that you do on your computer and share it with hackers who control them. One mistake opening an attachment, visiting a rogue website, or hitting the wrong link and you’re a victim. It’s a simple way for hackers to steal your data and account credentials.
The free Ghostpress download scans for existing keyloggers on your computer and offers real-time protection. It runs in the background while you type and also blocks background attempts to record your activities.
Are you using a Mac? Tap or click here for tips on spotting and removing keyloggers.
5. Only use encrypted connections
When shopping online, you know to look for web addresses that start with “https://”. This assures you that the website is transferring data over a secure encrypted connection. You'll also see a lock icon in your browser’s address bar.
This encryption guards against hijacking and malicious hacking attempts, but not every site has made the switch. Take matters into your own hands. You can remember only to visit mainstream sites and look for the lock.
Alternatively, add the free HTTPS Everywhere browser extension to your security arsenal. It rewrites your web requests as secure, even if the website you visit isn't adequately encrypted.
And one more, don’t forget your cameras.
We’ve all heard the horror stories of someone hacking into a security camera watching over a home or nursey. Take action now before you become a victim. Many security cameras offer increased security settings and two-factor authentication.
What digital lifestyle questions do you have? Call Kim's national radio show and tap or click here to find it on your local radio station. You can listen to or watch The Kim Komando Show on your phone, tablet, television or computer. Or tap or click here for Kim's free podcasts.
How To Make Sure Your Mac Isn T Hacked Password
Copyright 2020, WestStar Multimedia Entertainment. All rights reserved.
How To Make Sure Your Mac Isn't Hacked
Learn about the latest technology on the Kim Komando Show, the nation's largest weekend radio talk show. Kim takes calls and dispenses advice on today's digital lifestyle, from smartphones and tablets to online privacy and data hacks. For her daily tips, free newsletters and more, visit her website at Komando.com.